DATE: 2025-11-21
CLEARANCE: L3-INTERNAL
0.0 EXECUTIVE SUMMARY
- Self-sovereign inheritance chain (Heirs ≠ Owners).
- The "Sunset Protocol" (Transition to cultural heritage).
- Biological Anchoring (DNA Hash authentication).
- Immutable "Write-Once" Memory Segments.
1.0 SCOPE & DEFINITION
This document specifies the technical architecture for the Heritable Digital Entity (HDE). The system is designed to preserve Human Digital Identity integrity for a minimum duration of 100+ years in a zero-trust environment.
OBJECTIVE: To create a sovereign, encrypted, decentralized container for human personality data that functions independently of any single corporate entity.
2.0 NORMATIVE REFERENCES
| Standard | Application |
|---|---|
| RFC 8493 | BagIt File Packaging Format (Library of Congress) |
| NIST SP 800-38D | AES-256-GCM Encryption Standards |
| ISO/IEC 29150 | Privacy Architecture Framework |
| Shamir's Scheme | (t, n) Threshold Cryptography (Split Keys) |
3.0 ARCHITECTURE TOPOLOGY
3.1 STORAGE HIERARCHY (The "Where")
The HDE is not stored in a centralized cloud. It utilizes a Local-First, Distributed-Backup topology.
- NODE A (MASTER): User's Physical Device (Encrypted Local Storage). Full Read/Write authority.
- NODE B (SHARDS): Distributed Hash Table (DHT) network (IPFS/Arweave). Data is split into encrypted 64MB chunks. No single node possesses a readable file.
- NODE C (COLD): Offline "Air-gapped" servers in Worms, Germany (Bunker storage on M-DISC optical media).
3.2 DATA TRANSMISSION
All data in transit is wrapped in TLS 1.3 tunnels. Handshakes occur via P2P (Peer-to-Peer) protocols, bypassing central routing servers to prevent "Man-in-the-Middle" attacks.
>> APPENDIX A: INTERFACE VISUALIZATION (PROTOTYPE V.5)
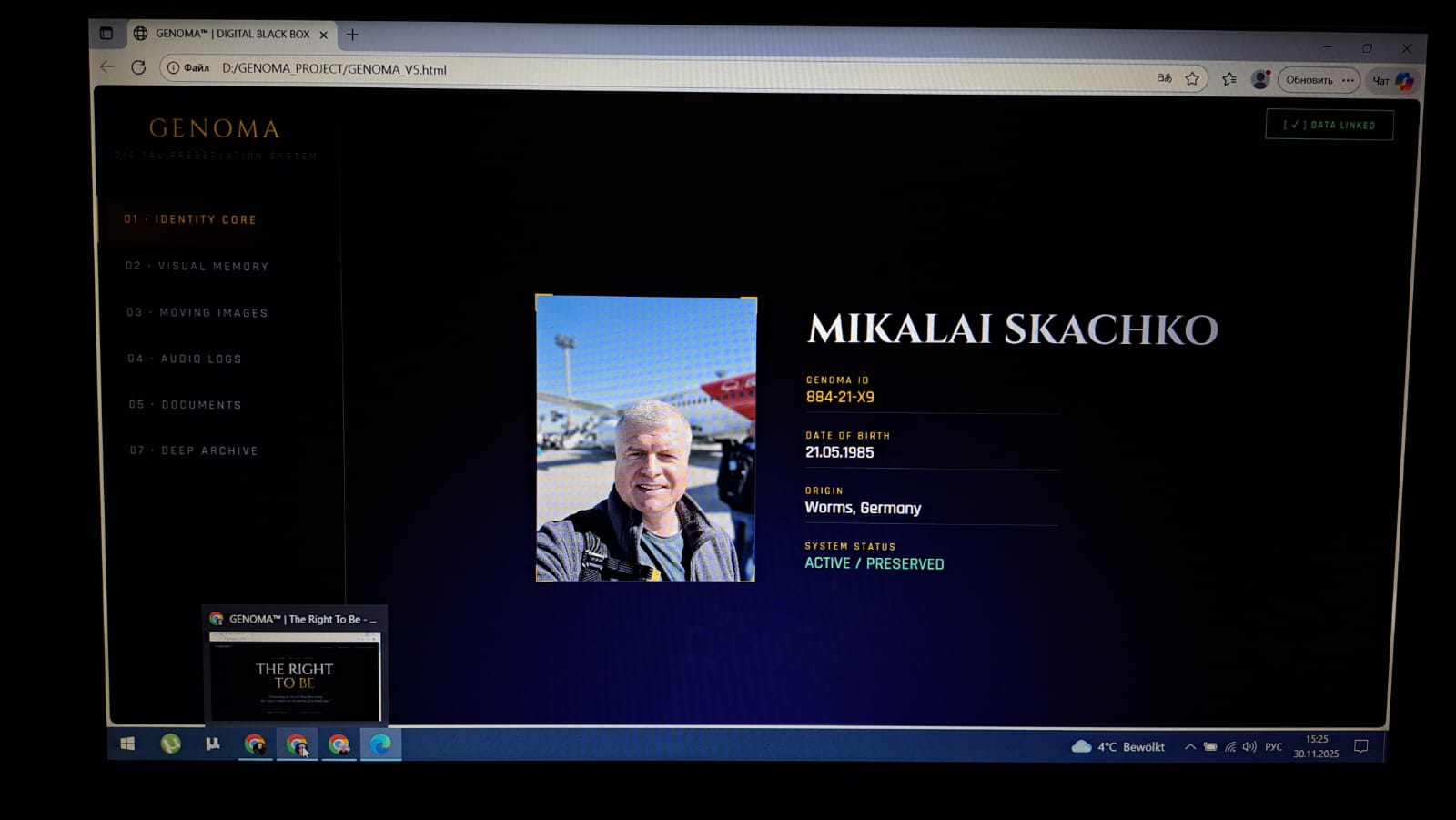
FIG 1.0: IDENTITY CORE (BIO-LINKED)
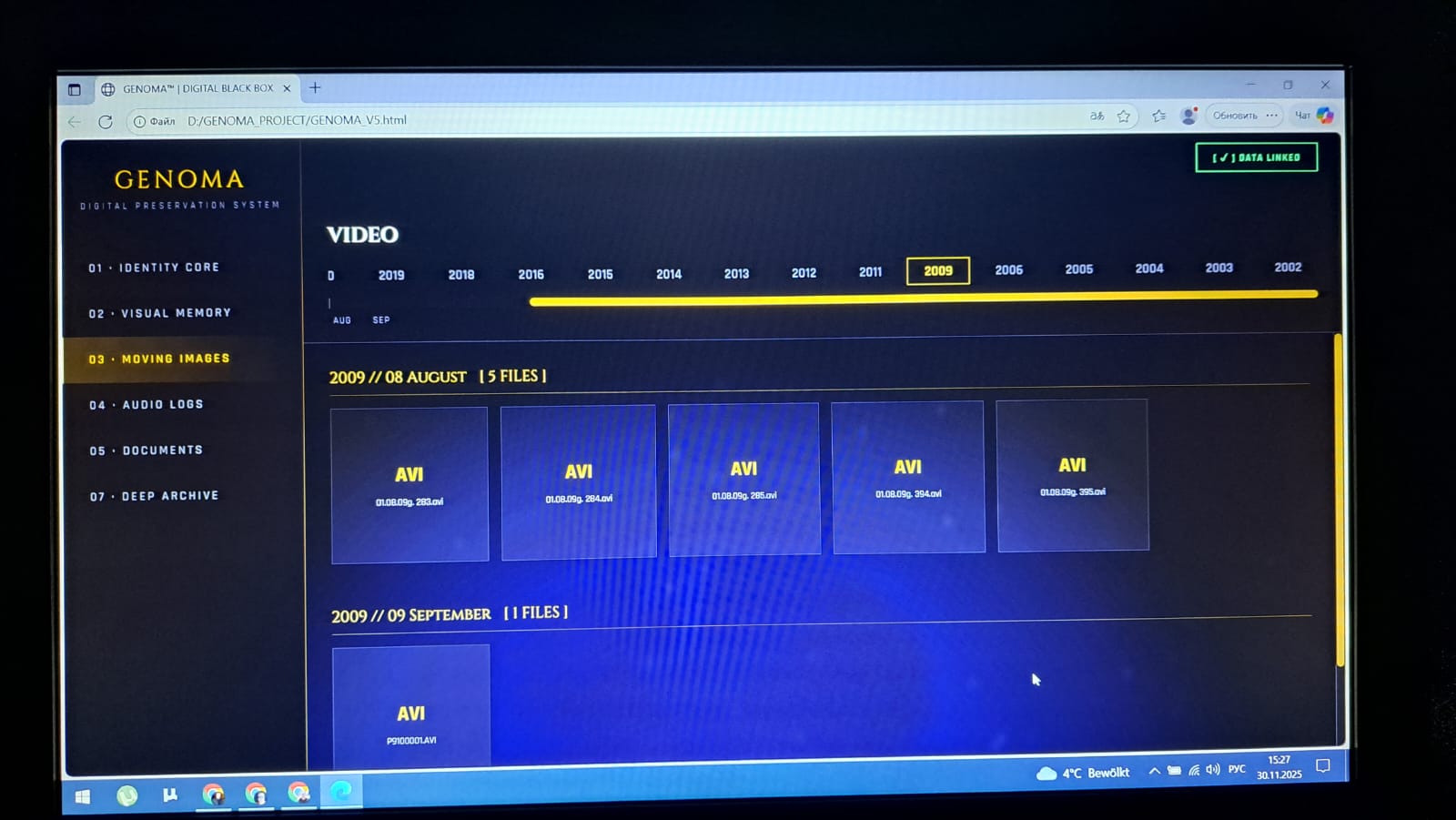
FIG 2.0: CHRONOLOGICAL MATRIX
4.0 CRYPTOGRAPHY & ACCESS
4.1 SECRET SHARING (SSSS Protocol)
To mitigate the risk of lost passwords or centralized theft, the Master Decryption Key is mathematically dismantled using Shamir’s Secret Sharing Scheme ($k=3, n=5$).
- Shard 1: User Biometrics (Local Secure Enclave)
- Shard 2: Physical NFC Token (YubiKey or similar)
- Shard 3: GENOMA Custody Server (Europe)
- Shard 4: GENOMA Custody Server (Asia)
- Shard 5: Designated Heir's Device (Inactive until trigger)
RECONSTRUCTION: Access requires any 3 shards. (e.g., User + Server EU + Server Asia).
5.0 LIFE-CYCLE STATES
| State ID | Description | Access Level |
|---|---|---|
| 01_GENESIS | Creation & Upload phase. | OWNER: R/W HEIR: NONE |
| 02_ACTIVE | Living state. Constant synchronization. | OWNER: R/W HEIR: LOCKED |
| 03_TRANSITION | Biological death confirmed via Oracle. | SYSTEM: FREEZE DATA |
| 04_LEGACY | Post-mortem operation. | OWNER: REVOKED HEIR: READ_ONLY |
6.0 INTEGRITY & OBSOLESCENCE
100-YEAR HORIZON: To prevent file format obsolescence (e.g., .jpg or .mp4 becoming unreadable in 2125), the container includes a virtualization layer (WASM) capable of decoding its own contents.
PAR2 REDUNDANCY: The container includes 15% redundancy code. Up to 15% of the data can be corrupted (bit-rot) and logically reconstructed without loss.
Mikalai Skachko
/Signed/